$ silo claude
███████╗██╗██╗ ██████╗ ██╔════╝██║██║ ██╔═══██╗ ███████╗██║██║ ██║ ██║ ╚════██║██║██║ ██║ ██║ ███████║██║███████╗╚██████╔╝ ╚══════╝╚═╝╚══════╝ ╚═════╝
AI coding agents in isolated containers and lightweight VMs
github.com/leighmcculloch/silo
How I got here — the problem, what I tried, and what worked
See it in action
How silo works, config, backends, and the bigger picture
Give them access and accept the risk, or restrict them and lose the thing that makes them useful.
"permissions": { "allow": [
"Bash(git fetch:*)", "Bash(git diff:*)", "Bash(git log:*)",
"Bash(git show:*)", "Bash(git branch:*)", "Bash(git add:*)",
"Bash(git commit:*)", "Bash(git stash:*)", "Bash(git checkout:*)",
"Bash(git rebase:*)", "Bash(git merge:*)", "Bash(git push:*)",
"Bash(git pull:*)", "Bash(git clone:*)", "Bash(git remote:*)",
"Bash(gh pr view:*)", "Bash(gh pr list:*)", "Bash(gh pr create:*)",
"Bash(gh pr checkout:*)", "Bash(gh pr merge:*)", "Bash(gh api:*)",
"Bash(gh issue view:*)", "Bash(gh issue list:*)", "Bash(gh issue create:*)",
"Bash(gh run view:*)", "Bash(gh run list:*)", "Bash(gh run watch:*)",
"Bash(cargo build:*)", "Bash(cargo test:*)", "Bash(cargo run:*)",
"Bash(cargo clippy:*)", "Bash(cargo fmt:*)", "Bash(cargo check:*)",
"Bash(go build:*)", "Bash(go test:*)", "Bash(go run:*)",
"Bash(go vet:*)", "Bash(go mod:*)", "Bash(go install:*)",
"Bash(npm install:*)", "Bash(npm test:*)", "Bash(npm run:*)",
"Bash(npx:*)", "Bash(deno run:*)", "Bash(deno test:*)",
"Bash(make:*)", "Bash(cmake:*)", "Bash(docker build:*)",
"Bash(docker run:*)", "Bash(docker compose:*)", "Bash(kubectl:*)",
"Read(~/.cargo/**)", "Read(~/.local/go/pkg/mod/**)",
"Read(~/.rustup/**)", "Read(~/.npm/**)", "Read(~/.config/**)",
"Write(~/Library/Caches/go-build/**)", "Write(~/.cargo/registry/**)",
"Write(~/Library/Caches/Homebrew/**)", "Write(~/.npm/_cacache/**)"
]}
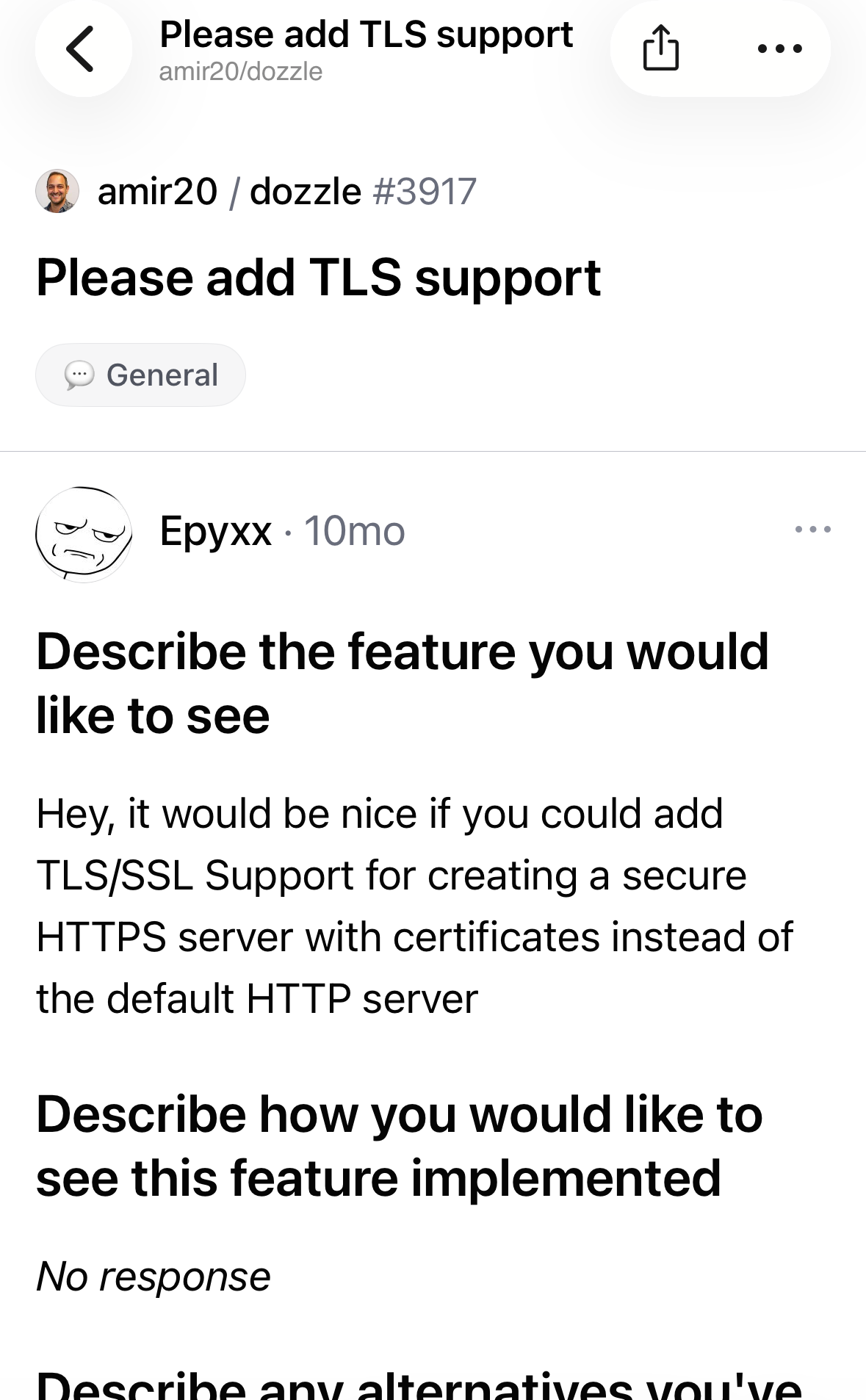
Felt thorough. But one permitted gh api call and an agent commented on a random GitHub discussion completely unrelated to my work.
sandbox-exec and custom rulesA CLI tool that runs AI coding agents in isolated containers and lightweight VMs — so they get full access without touching our machine.
The agent runs in yolo mode with full capability — but only inside an isolated container with access to our working directory.
What happens when you run silo claude
Anthropic's CLI for Claude
silo claude
AI coding CLI
silo opencode
GitHub's Copilot in the terminal
silo copilot
Auto-detected: uses Apple Container if installed, falls back to Docker.
Ubuntu 24.04, build-essential, pkg-config
Node.js, Go, Rust (latest stable)
git, GitHub CLI, Docker CE, jq, zsh
gopls, rust-analyzer
github-mcp-server pre-installed
Auto-configured from our host
Same filesystem layout as host
Continue the same session locally — with full access to API keys, GitHub tokens, and everything else on our machine.
Images tagged by hash of Dockerfile + tool + build args. Only rebuilt when something changes.
github.com/leighmcculloch/silo
Apache 2.0 · macOS · Docker & Apple Containers